Stopping the Flood: How to Combat Card Testing Attacks on Your Clients' Stores
You know that feeling when a client's store, usually humming along with a steady stream of orders, suddenly starts screaming? That's exactly what happened to one community member recently, describing a nightmare scenario: hundreds, even thousands, of failed payments hitting their site in a short period. What's going on here? As many respondents quickly pointed out, this is almost certainly a 'card testing' attack.
The Silent Threat: What Are Card Testing Attacks?
Card testing, or 'carding,' is when malicious scripts use automated bots to test the validity of stolen credit card numbers. They blast payment gateways with card details, usually with small transaction amounts, to see which ones go through. If a card is valid, it's then sold on the dark web for larger fraudulent purchases. For your clients' stores, this means a deluge of failed transactions, often far exceeding their typical daily order volume.
The original poster initially noted that these failed payments weren't costing them money directly. While that's a relief in the short term, several community members were quick to highlight the hidden dangers. One expert warned, "Most payment gateways are charging you a fee for each failed payment. This could be burning money quickly." Another added a critical point: "Still it is a good idea to see if you can block... eventually some fraud thresholds were reached on our gateway's side of things and our card processing was halted."
Beyond potential direct fees or gateway suspension, these attacks consume server resources, flood inboxes with unnecessary emails, and, as one person put it, create 'stress.' In a more complex setup, they can also seriously skew analytics, making it harder to track legitimate customer behavior.
Your Agency's Playbook: Stopping the Onslaught
So, what can agencies do when their clients are under fire? The community discussion offered a wealth of actionable strategies. It's not just about one fix; it's about layered defense.
1. Server-Level & Site Configuration
- Block IPs: One of the first suggestions was to "ban the IP addresses at least temporarily." Blocking ranges at the server level for about 30 days can often deter attackers, as their systems learn to move to 'softer targets.'
- CAPTCHA/Turnstile on Checkout: This was a resounding recommendation. As one community member stated, "The main goal here is to stop the bots before they even get a chance to reach the payment form and keep hammering your checkout." Implementing a CAPTCHA or Turnstile on the checkout page is a powerful bot deterrent.
- Rate Limiting: If your client's store uses the Checkout Block or Store API, ensure rate limiting is turned on. This prevents a single IP or user from making too many attempts in a short timeframe.
- Prevent Direct Cart Access: Some bots bypass product pages entirely and go straight to the cart. Blocking this behavior can stop some automated scripts.
- Dedicated Plugins: For WooCommerce users, a specific plugin like Checkout Shield for WooCommerce was recommended as a free solution to stop this issue completely.
- Require Account Login (Situational): A more restrictive approach, suggested by a respondent, is to require account login or creation before checkout. This isn't suitable for all businesses but can be a strong barrier for bots if the client's business model allows for it.
2. Payment Gateway Power Plays
Your payment gateway isn't just a transaction processor; it's a fraud prevention partner. Many gateways offer robust tools:
- Adjust Fraud Velocity Rules: For gateways like Stripe or PayPal, jump into the settings and "crank up the fraud velocity rules immediately." These rules let you define how many failed attempts from a single card or IP are allowed within a certain period before transactions are blocked.
- Communicate with Your Gateway: If thresholds are being hit or you're seeing unusual activity, reach out to your gateway's support. They can often provide insights, adjust settings on their end, or offer additional tools.
Leveraging Your Agency's Knowledge Base
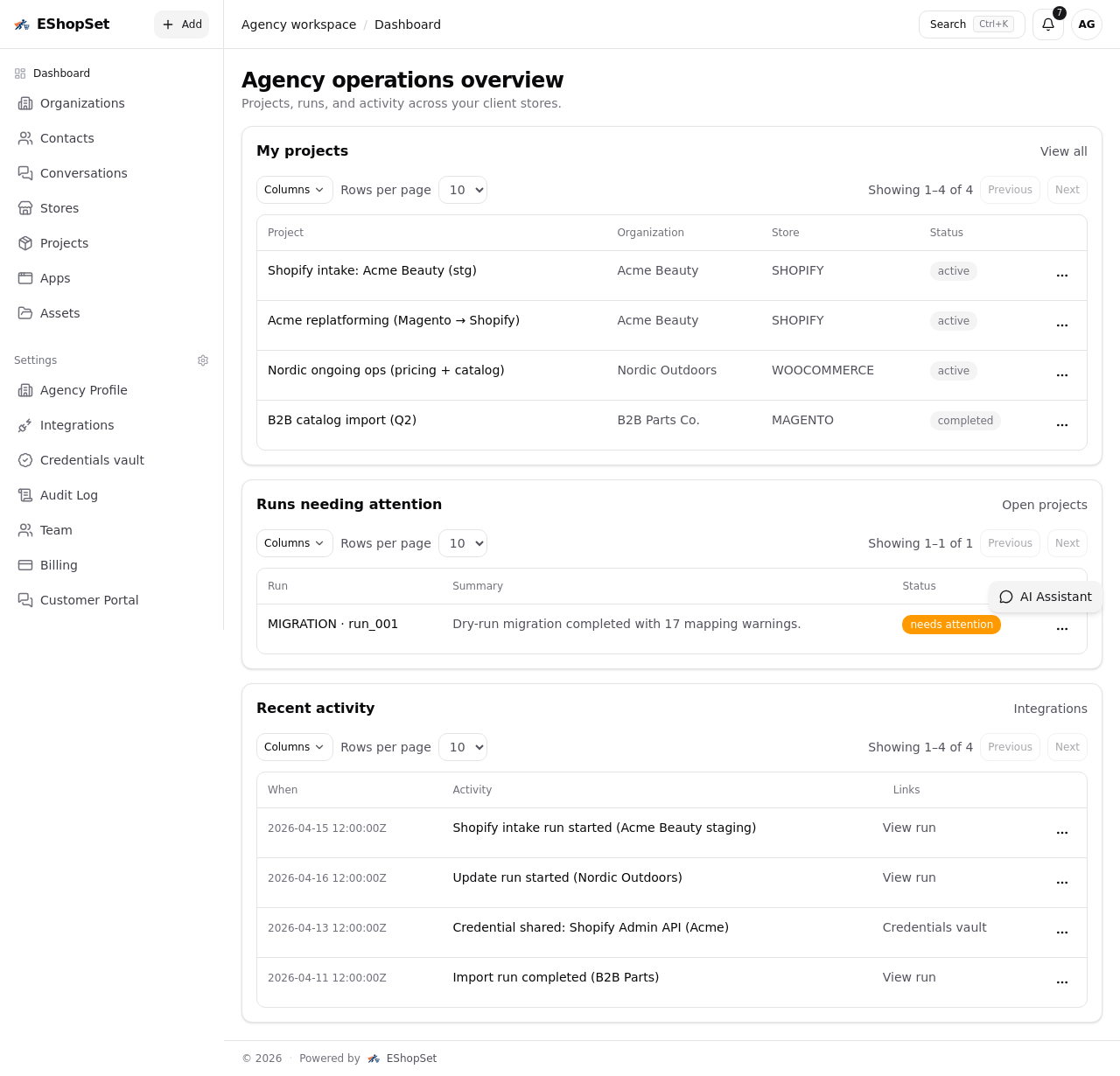
For agencies, dealing with these attacks isn't a one-off. It's a recurring challenge across client portfolios. This is where a robust implementation artifacts library becomes invaluable. Documenting your successful strategies – the specific CAPTCHA configurations, the server-level IP blocking scripts, the optimal payment gateway fraud settings – creates a reusable asset. When a new client faces this issue, your team isn't starting from scratch; they're deploying proven solutions from your internal knowledge base.
EShopSet Team Comment
This discussion highlights a critical, often underestimated, aspect of ecommerce security. While the immediate financial impact might not always be apparent, card testing attacks are a drain on resources and a serious risk to payment processing stability. Agencies absolutely must be proactive here. Implement CAPTCHA and strong fraud rules as a baseline for all new client setups, and have a clear, documented response plan for when these attacks inevitably occur. Don't wait for your client's processing to be halted before acting.
Dealing with card testing attacks is an ongoing part of managing a healthy ecommerce operation. By combining server-level defenses, robust site configurations, and smart payment gateway settings, your agency can build resilient stores that protect your clients from these digital nuisances and far more serious threats.