Securing Your Ecommerce Data: A Deep Dive into Server-to-Server API Integrations
Hey EShopSet community! We've all been there: building out custom integrations for clients, pushing order data from one system to another, and then that little voice in the back of your head pipes up – "Is this truly secure? Am I exposing sensitive customer information?" It's a critical question, and one that recently sparked a great discussion in an online developer community.
The original poster brought up a very practical scenario: using a WooCommerce hook, PHP, and cURL to send a request authenticated with an X-API-KEY header to a third-party service. Their core question was, "Would this be considered a secure approach for preventing exposure of customer data to attackers?" Let's break down the expert consensus and what it means for your agency's operations, especially when dealing with sensitive customer data for platforms like HubSpot Commerce or CRM.
The Core Principle: Server-to-Server Communication is Paramount
The good news is, the community was largely in agreement: yes, this approach, when implemented correctly, is generally considered secure. One respondent quickly confirmed, "Yes — server-to-server requests using PHP/cURL with an X-API-KEY header are generally much safer than exposing anything client-side in JavaScript." Another community member echoed this, stating, "Yeah, that’s a pretty standard setup and generally secure if everything is server-to-server over HTTPS."
The key takeaway here is server-to-server communication. When your server talks directly to another server, without the client's browser ever seeing the sensitive credentials or data in transit, you're already miles ahead in terms of security. This is fundamentally different from making AJAX calls from a user's browser, where API keys and data can be intercepted or exposed more easily. For agencies managing complex ecommerce migration project management, understanding this fundamental difference is crucial for maintaining data integrity and client trust.
Beyond the Basics: Essential Safeguards for Robust Security
While server-to-server is a strong foundation, the experts were quick to highlight several crucial best practices that turn a "generally secure" setup into a robust one. Think of these as your agency's security checklist when developing or managing integrations.
Always Use HTTPS
This might seem obvious, but it's the bedrock of secure online communication. HTTPS encrypts data in transit, protecting it from eavesdropping and tampering. Ensure all your API endpoints, both sending and receiving, strictly enforce HTTPS. Without it, even the most robust API key management can be undermined.
API Key Management: Your Digital Fortress
The X-API-KEY header is only as secure as the key itself. Here's how to manage it:
- Strictly Server-Side: As multiple community members emphasized, the API key must never touch frontend code (HTML, JavaScript, browser console, AJAX responses). It should reside only on your server.
- Environment Variables: Store API keys as environment variables, not hardcoded in your application's source code. This prevents them from being exposed in version control systems and makes deployment more secure.
- Dedicated API Users/Roles: If the third-party service allows, create specific API users or roles with the minimum necessary permissions (least privilege) for the integration.
- Key Rotation: Implement a strategy for regularly rotating API keys. If a key is compromised, its lifespan is limited.
- Avoid Logging Sensitive Payloads: Do not log the API key or sensitive customer data (like full credit card numbers, even if masked) in plain text anywhere, especially in publicly accessible logs.
Data Minimization and Validation: The Principle of Least Privilege for Data
When transmitting order data, or any customer information, adhere to these principles:
- Send Only What's Necessary: Minimize the amount of customer data you send. If a third-party service only needs an order ID and total, don't send the customer's full address and payment details. This reduces the attack surface.
- Validate and Sanitize Incoming Data: Before processing any data received from an external API, always validate and sanitize it. This prevents injection attacks and ensures data integrity.
- PII and Compliance: Be acutely aware of Personally Identifiable Information (PII) and compliance regulations like GDPR and CCPA. When integrating with platforms like HubSpot CRM or HubSpot Commerce, ensure your data mapping and transmission practices align with these regulations, especially when dealing with customer profiles or order histories.
Secure Logging and Error Handling
While logging is essential for debugging and monitoring, it can also be a security risk if not handled carefully. Ensure your error logs do not capture sensitive customer data or API keys. Implement masking or redaction for any potentially sensitive information before it's written to logs.
Proactive Monitoring and Auditing
Security isn't a one-time setup; it's an ongoing process. Regularly monitor your API call logs for unusual activity, failed authentication attempts, or excessive data transfers. Conduct periodic security audits and consider penetration testing for critical integrations to identify vulnerabilities before attackers do.
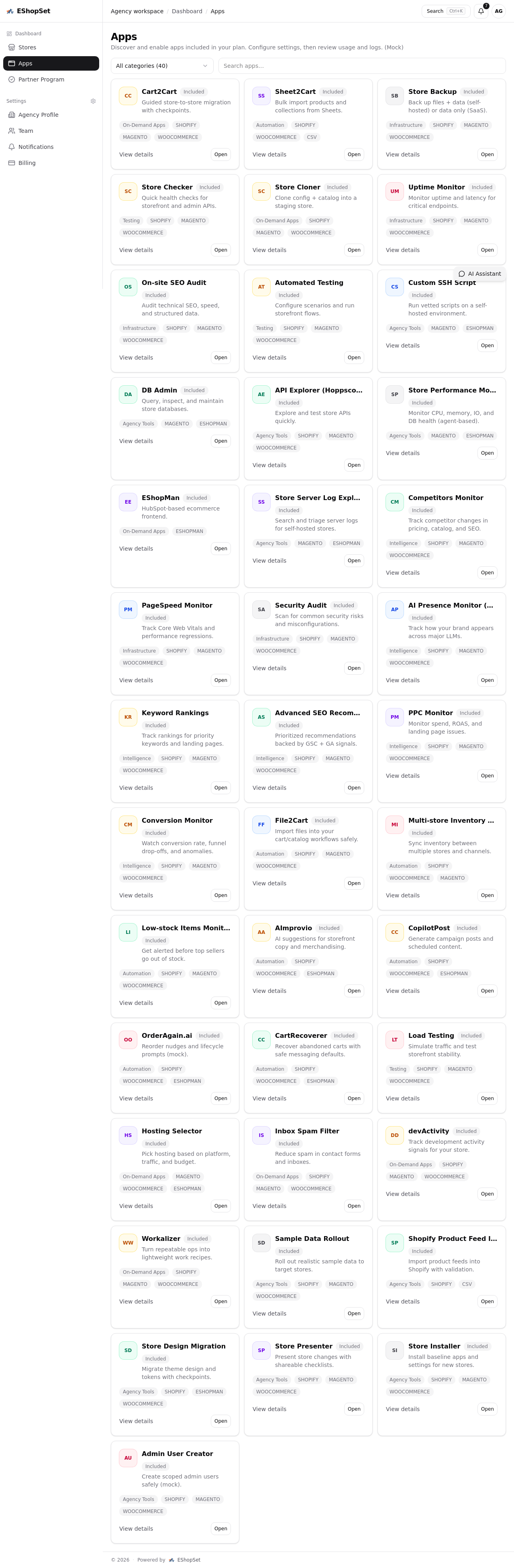
EShopSet and Your Secure Agency Workflow
At EShopSet, we understand the complexities and critical importance of secure data handling for ecommerce agencies. Whether you're managing an ecommerce migration project management for a new client or optimizing existing agency workflow automation, secure API integrations are the backbone of reliable operations.
Our platform helps agencies orchestrate these complex integrations, providing the oversight and tools needed to ensure data flows securely and efficiently between diverse systems. Imagine seamlessly pushing order data from a client's custom storefront to HubSpot Commerce for streamlined order fulfillment, or updating customer profiles in HubSpot CRM without ever compromising sensitive information. EShopSet empowers your team to build robust, compliant, and secure solutions, giving you peace of mind and allowing you to focus on delivering exceptional results for your clients' RevOps strategies.
Conclusion
The consensus from the developer community is clear: server-to-server API communication, when implemented with rigorous security best practices, is a highly effective way to protect sensitive customer data. By prioritizing HTTPS, meticulous API key management, data minimization, and continuous monitoring, your agency can build integrations that are not only functional but also fundamentally secure.
Embrace these principles to safeguard your clients' data, maintain trust, and elevate your agency's reputation as a leader in secure ecommerce solutions. With EShopSet, you have a partner dedicated to helping you achieve these high standards in every project.