Securing Your Client's Storefront: Proactive Measures Against Card Testing Fraud
Hey EShopSet community!
In the dynamic world of ecommerce, agencies are constantly navigating new challenges to protect their clients' businesses. One particularly insidious threat that has surged recently is card testing — a type of fraud where malicious actors use automated bots to validate stolen credit card numbers by making small, often numerous, purchases on live storefronts. This isn't just a minor annoyance; it's a serious threat to a store’s financial health, payment processor standing, and overall reputation.
Recently, a buzzing discussion caught our eye in an ecommerce community forum. The original poster was in a bind, dealing with a wave of card testing attacks that had actually resulted in fraudulent orders going through their PayPal gateway. To make matters worse, PayPal’s resolution center was glitching, leaving them stuck with bad payments and no clear path to report them. This scenario, unfortunately, is all too common and underscores the critical need for robust security protocols within every ecommerce operation.
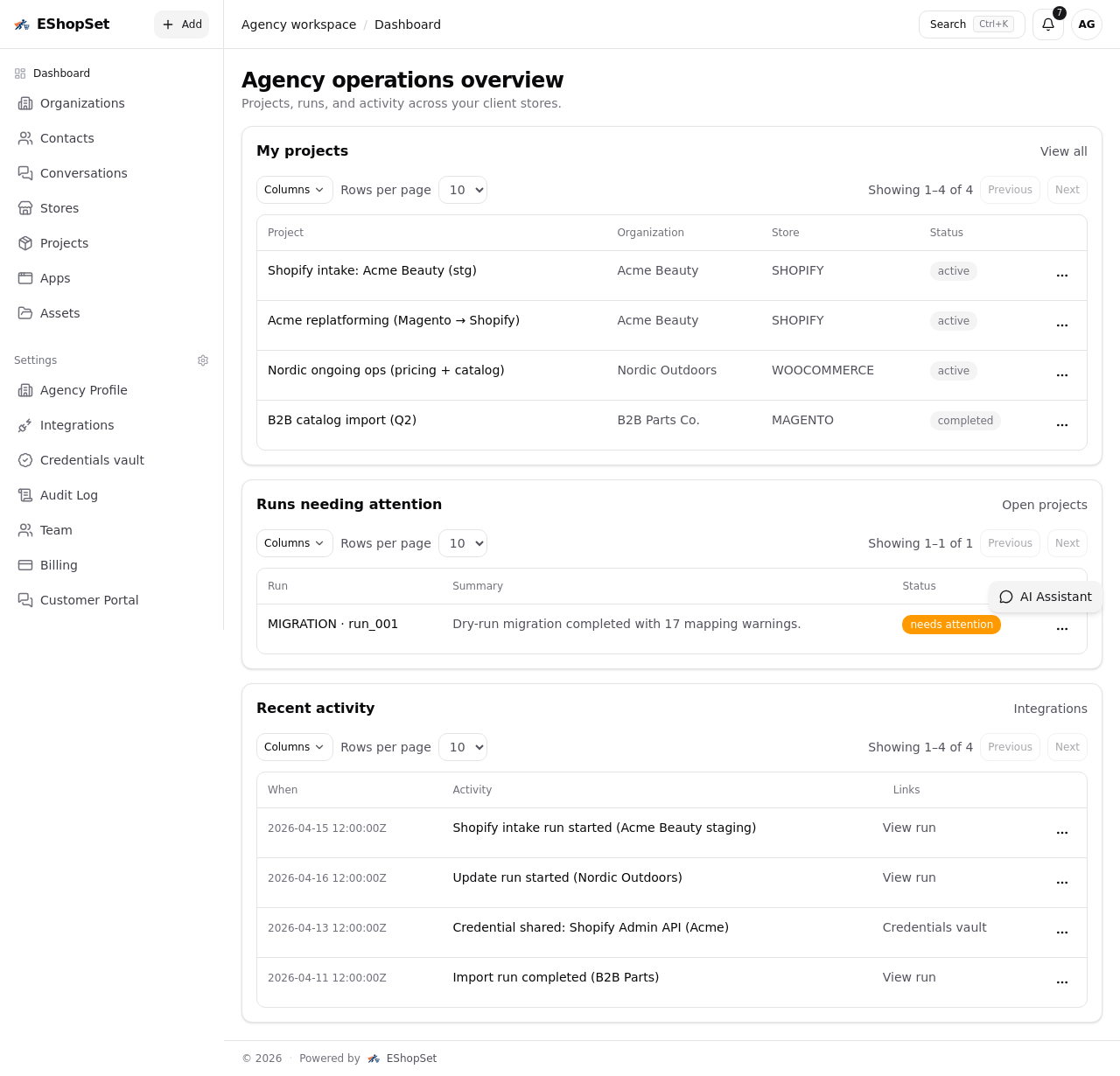
As a Senior Tech Writer at EShopSet, an operations workspace designed to empower ecommerce agencies, we understand these pain points deeply. Let's dive into the collective wisdom shared by the community and distill some actionable advice for agency owners, project managers, and developers managing client stores, ensuring their operations are resilient against such sophisticated attacks.
The Immediate Crisis: When Fraudulent Orders Go Through
The core problem faced by the original poster was clear: card testing bots had successfully processed payments, and they couldn't report them. The immediate question was, "What do I do now?"
Refund, Refund, Refund (and Why It's Crucial)
The overwhelming consensus from the community was crystal clear: refund immediately. Multiple respondents, citing advice from payment giants like Stripe and PayPal themselves, stressed this urgency. Why?
- Avoid Chargebacks: If you don't refund promptly, the legitimate card owner will eventually notice the fraudulent transaction and initiate a chargeback. This not only costs the merchant the money but also a hefty chargeback fee (a community member noted PayPal charges around $15, for example). Stripe also explicitly recommends immediate refunds to prevent disputes, as detailed in their documentation.
- Protect Your Account: As one community member ominously warned, "You run a serious risk of being banned from PayPal if this continues to happen." Payment processors monitor chargeback rates closely. High rates signal risk and can lead to account suspension or even termination, crippling a client's ability to process payments.
- Minimize Financial Loss: While refunding means losing the processing fee, it prevents the potentially larger loss of both the product (if shipped) and the chargeback fee.
When payment processor interfaces glitch, as the original poster experienced, direct contact with support becomes paramount. Community members suggested trying different browsers or contacting support directly via phone or chat to manually flag transactions. For agencies, this highlights the need for robust internal processes. Leveraging an operations workspace like EShopSet, which integrates with client communication tools and project management, can help agencies log these incidents, track support tickets with payment gateways, and ensure timely follow-up, even when external systems fail.
Proactive Defense: Securing Your Client's Storefront
While immediate refunds address the symptom, the real solution lies in preventing card testing attacks from reaching the payment gateway in the first place. This requires a multi-layered security approach.
1. Robust Bot and Traffic Management
- Web Application Firewalls (WAF) & CDN: Placing your client's website behind a service like Cloudflare (as suggested by several community members) offers a powerful first line of defense. Cloudflare's WAF can block known malicious IPs, filter suspicious traffic, and even geo-block countries where you don't sell.
- CAPTCHA & Bot Detection: Implement solutions like Cloudflare Turnstile or other advanced CAPTCHAs on checkout pages. Community members also recommended plugins like OOPSpam (with its "Block orders from unknown origin" setting), kkey Protect, TrustLens, and Checkout Shield. These tools are designed to differentiate between human users and automated bots.
- IP Reputation & Proxy Detection: As one savvy community member pointed out, modern card testing bots often use residential proxies, making simple geo-blocking less effective. Solutions like ipasis.com (mentioned in the thread) focus on checking IP reputation, rejecting traffic from known data centers or suspicious proxy ranges before the payment even hits the gateway. This is a crucial, often overlooked, layer of defense.
2. Payment Gateway Configuration & Best Practices
The original poster's frustration with PayPal allowing orders through despite a card and delivery postal code mismatch highlights a critical vulnerability. Agencies must ensure their clients' payment gateways are configured for maximum security:
- Address Verification System (AVS) & CVV Checks: Ensure these are strictly enforced. AVS checks the billing address provided against the cardholder's address on file, while CVV verifies the 3 or 4-digit security code. Mismatches should ideally trigger declines or high-risk flags.
- Fraud Filters & Rules: Most payment processors offer customizable fraud filters. Agencies should work with their clients to set up rules based on transaction value, IP address, shipping/billing address discrepancies, purchase frequency, and other behavioral patterns.
- Consider Alternatives: As some community members expressed, if a payment gateway consistently fails to provide adequate protection or responsive support, it might be time to explore more reliable alternatives that offer better fraud prevention and seller protection.
3. Leveraging HubSpot for Enhanced Security & Operations
For agencies managing multiple client storefronts, integrating security measures with a powerful platform like HubSpot is key to a holistic RevOps strategy. EShopSet facilitates this by streamlining operations and providing a centralized view.
- HubSpot Commerce & CRM Integration: While HubSpot Commerce provides robust storefront capabilities, integrating it with advanced fraud detection tools ensures that suspicious activities are flagged early. Any fraudulent orders that do slip through can be immediately identified within the HubSpot CRM. Agencies can create custom properties or workflows to automatically tag these orders, notify relevant team members via Sales Hub, and trigger actions like pausing fulfillment.
- Proactive Monitoring with Workflows: HubSpot workflows can be configured to monitor for patterns indicative of card testing, such as multiple failed payment attempts from a single IP address, unusual order values, or rapid succession of orders. These workflows can then send internal alerts, update client records, or even automatically adjust customer segments.
- Secure Client Portal with RBAC: This is where rbac for client portal becomes indispensable. EShopSet, as an operations workspace, can integrate with HubSpot to provide a secure client portal where agencies can share real-time security reports, incident logs, and demonstrate proactive measures taken. Implementing robust rbac for client portal ensures that clients only see relevant security summaries and operational dashboards, while agency team members have the appropriate permissions to manage security settings, respond to incidents, and access sensitive data. This granular control is vital for maintaining data integrity and client trust.
// Example pseudo-code for a HubSpot workflow trigger for fraud detection
IF (Order.PaymentStatus == "Failed" AND Order.Attempts > 3 AND Order.IPAddress == PreviousOrder.IPAddress)
THEN
Set Order.FraudRisk = "High"
Send Internal Notification to "Security Team"
Create Task for "Client Manager" to review order
Update Client.SecurityStatus = "Alert"
Conclusion: A Proactive Stance for Agency Success
Card testing attacks are a persistent threat in the ecommerce landscape, but they are not insurmountable. By adopting a proactive, multi-layered security strategy—combining robust bot protection, vigilant payment gateway configuration, and intelligent use of platforms like EShopSet and HubSpot—agencies can significantly reduce their clients' exposure to fraud.
Beyond technical implementations, fostering clear communication with clients about security risks and establishing transparent protocols for incident response is paramount. Leveraging an integrated operations workspace ensures that security isn't an afterthought but a core component of your agency's service offering, protecting both your clients' bottom line and your agency's reputation. Stay vigilant, stay secure, and let EShopSet empower your agency to navigate these challenges with confidence.