Protecting Your Ecommerce Clients from Card Testing Attacks: An Agency's Guide
The Silent Threat: What Are Card Testing Attacks?
Imagine a client's online store, usually a picture of steady growth, suddenly barraged by thousands of failed payment attempts in a single day. This alarming scenario, recently shared by a community member, is a classic 'card testing' attack. Malicious actors use automated scripts to validate stolen credit card numbers by running them through payment gateways with small, often failed, transactions. Successful cards are then sold on the dark web for larger fraudulent purchases.
While the original poster initially noted no direct charges for these failed attempts, the broader community quickly highlighted the insidious, hidden costs. As one expert warned, "Most payment gateways are charging you a fee for each failed payment. This could be burning money quickly." Another critical point emerged: "Still it is a good idea to see if you can block... eventually some fraud thresholds were reached on our gateway's side of things and our card processing was halted." This means not only potential financial drain but also the risk of a complete shutdown of payment processing for your client's legitimate customers.
Beyond direct fees or gateway suspension, these attacks consume precious server resources, flood inboxes with unnecessary notifications, and, as one person aptly put it, create 'stress.' For agencies managing complex commerce setups with HubSpot Commerce, card testing can severely skew analytics, making it challenging to track legitimate customer behavior, assess campaign performance, and maintain accurate RevOps reporting. This noise impacts everything from sales forecasting to inventory management, undermining the very data integrity your agency relies on.
Your Agency's Playbook: Stopping the Onslaught
When your clients are under fire, a multi-layered defense is crucial. The community discussion provided a wealth of actionable strategies that agencies can implement:
- IP Blocking at the Server Level: A fundamental first step. Temporarily blocking IP addresses or ranges identified as sources of attack can deter bots. As a community member suggested, "blocking the IP ranges at the server level for around 30 days will stop a lot of future attempts."
- CAPTCHA or Turnstile on Checkout: This is a highly effective barrier. By adding a CAPTCHA or similar bot-detection mechanism before the payment form, you can stop automated scripts from even reaching the payment gateway. "The main goal here is to stop the bots before they even get a chance to reach the payment form and keep hammering your checkout," advised one contributor.
- Rate Limiting: Implement rules that restrict the number of checkout attempts from a single IP address or user within a specific timeframe. This prevents bots from rapidly cycling through card numbers.
- Block Direct Cart Access: Some bots bypass product pages and go straight to the cart or checkout. Configure your store to require a visit to a product page before adding items to the cart or proceeding to checkout.
- Require Account Login/Creation: While potentially adding friction for legitimate customers, requiring an account for checkout can significantly deter bots, as creating multiple accounts is more complex than simply submitting payment forms.
- Leverage Payment Gateway Fraud Settings: Most major gateways (Stripe, PayPal, Square, etc.) offer built-in fraud detection and prevention tools. "Jump into your Stripe or PayPal settings and crank up the fraud velocity rules immediately," recommended a community member. These settings can often detect and block suspicious patterns automatically.
- Utilize Security Plugins/Extensions: For platforms like WooCommerce, dedicated plugins (e.g., "Checkout Shield for WooCommerce" mentioned in the thread) can provide robust, out-of-the-box protection against card testing and other forms of checkout fraud.
These measures are not just about stopping attacks; they're about preserving the integrity of your client's storefront and the valuable data it generates for their RevOps strategy.
 Leveraging Your Operations Workspace for Enhanced Security
Leveraging Your Operations Workspace for Enhanced Security
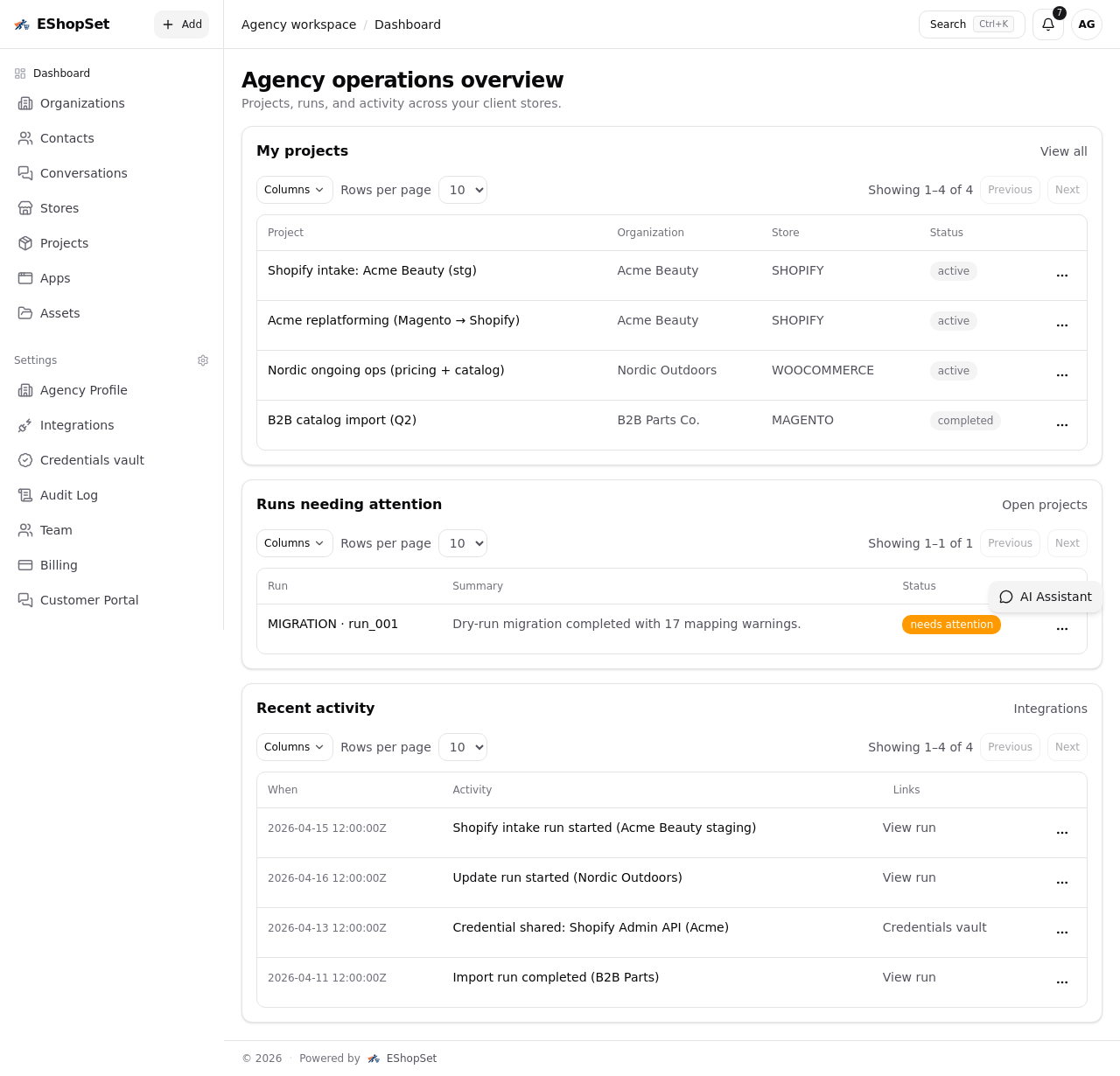
For ecommerce agencies, managing security across multiple client stores can be a complex endeavor. This is where a robust operations workspace like EShopSet becomes indispensable. It allows your team to implement and monitor these security measures efficiently and transparently.
With a role based access control client portal, your agency can configure intricate security settings for each client without granting them full, potentially overwhelming, backend access. This ensures that only authorized personnel can make critical security adjustments, while clients can still view high-level security reports and incident summaries through a streamlined interface. This centralized management is crucial for maintaining consistent security standards across your portfolio.
Furthermore, a linear client portal within your operations workspace can simplify communication around security incidents and resolutions. Instead of complex technical explanations, clients receive clear, concise updates on attacks detected, actions taken, and the current security posture. This transparency builds trust and demonstrates your agency's proactive approach to safeguarding their business.
Integrating these security insights with your client's HubSpot Commerce data is also vital. By preventing card testing attacks, you ensure that the data flowing into HubSpot for sales, marketing, and service is clean and accurate. This clean data is critical for effective RevOps, allowing your clients to make informed decisions based on genuine customer interactions, rather than noise from fraudulent attempts. The efficiency of any ecommerce delivery management software, for instance, relies heavily on accurate order data; card testing attacks can corrupt this data, leading to operational inefficiencies and wasted resources.
Beyond the Immediate Threat: Long-Term Security Posture
Stopping an active card testing attack is just the beginning. A comprehensive security strategy involves continuous vigilance:
- Regular Monitoring: Implement tools that constantly monitor for unusual activity, failed payment spikes, or suspicious IP addresses.
- Security Audits: Periodically review your client's store configurations, payment gateway settings, and server logs for vulnerabilities.
- Stay Informed: The landscape of cyber threats is constantly evolving. Keep abreast of new attack vectors and prevention techniques.
By taking a proactive and integrated approach to security, ecommerce agencies can not only protect their clients from immediate financial and operational harm but also build a resilient foundation for sustainable growth. Leveraging powerful platforms that offer centralized management and clear client communication is key to transforming potential threats into opportunities for stronger client relationships and more robust ecommerce ecosystems.