Heads Up, Agencies: A Critical cPanel Vulnerability Threatens Your Magento Client Backups
Hey everyone, let's talk about something serious that came up in a community discussion recently – a critical vulnerability that could be a huge headache for any agency managing Magento stores, especially those on shared cPanel hosting. We're talking about a potential nightmare scenario: an attacker gaining access to your client's server and, even worse, deleting their backups before anyone even knows there's a problem.
The original poster in this discussion brought to light CVE-2026-41940, a CVSS 9.8 vulnerability that cPanel patched in April 2026, but which was actively exploited as a zero-day since at least February of that year. Yikes. For us, this isn't just a technical detail; it's a massive risk to client trust, data integrity, and our agency's reputation.
Understanding the Threat: CVE-2026-41940 Explained
So, what exactly happened? This vulnerability allows an attacker to bypass cPanel authentication using something called CRLF injection. Once past cPanel, they get access to WHM – the WebHost Manager interface. For those unfamiliar, WHM is essentially the control panel for the server itself, not just an individual hosting account. And with WHM access, an attacker can do some truly damaging things:
- Delete or corrupt automated backups: This is the big one that kept the original poster up at night, and for good reason. Most merchants (and often, their agencies) assume server-side backups are safe. This exploit directly targets that assumption.
- Access files across all accounts on a shared server: If your client is on shared hosting, this means other clients' data could be exposed, and vice versa.
- Modify server configuration: Attackers could alter server settings, potentially creating backdoors or further compromising the environment.
The core issue here is that an attacker could wipe out server-side backups before anyone even realizes the breach has occurred. Imagine telling a client their site is compromised, and then having to add, "...and all our backups are gone." That's a conversation no agency wants to have.
Immediate Action for Agencies: What to Check Right Now
This kind of critical check highlights the absolute necessity of robust task tracking for agencies. We need to ensure these vital security steps aren't missed for any client. Based on the community discussion, here's a checklist of what you and your team should be looking into immediately for any Magento client on a cPanel host:
- Confirm Your Host Has Applied the Patch: This is step one. Reach out to your client's hosting provider (or your own, if you manage it directly) and ask them specifically if they've applied the cPanel patch for CVE-2026-41940. Don't assume; verify.
- Verify Off-Server Backups: This is non-negotiable. Ensure your client has robust, off-server backups that cPanel (and thus, an attacker with WHM access) cannot touch. Think Amazon S3, Backblaze, or similar cloud-based solutions. These should be part of every client's standard delivery playbooks.
- Check WHM Login Logs for Unusual Access: If you have WHM access for your client's server, or if your client can provide them, scrutinize the login logs for any unusual or unauthorized access during the exposure window (February 2026 onwards).
- Inquire About Account Isolation: If your client is on a shared host, ask the provider whether their account was isolated from other tenants during the vulnerability's exposure window. While a patch fixes the future, understanding past exposure is crucial.
The full technical disclosure is available from WatchTowr, and there's also an excellent write-up on the ecommerce-specific implications from Everyhost, which we found particularly useful:
Beyond the Immediate: Proactive Security & Backup Strategies
This incident is a stark reminder that even seemingly secure systems can have critical vulnerabilities. For agencies, this means going beyond reactive fixes and embedding proactive security into our operations. Having clear delivery playbooks for security audits and incident response isn't just good practice; it's essential for maintaining client trust and operational continuity.
Consider:
- Layered Backup Strategy: Always advocate for multiple backup layers: server-side (for quick restores), off-server (for disaster recovery), and even local copies for critical data.
- Regular Security Audits: Make security audits a routine part of your service offering, not just a response to a crisis.
- Dedicated Hosting or Managed Services: For larger Magento clients, moving away from shared cPanel hosting to more isolated or managed environments can significantly reduce risk exposure.
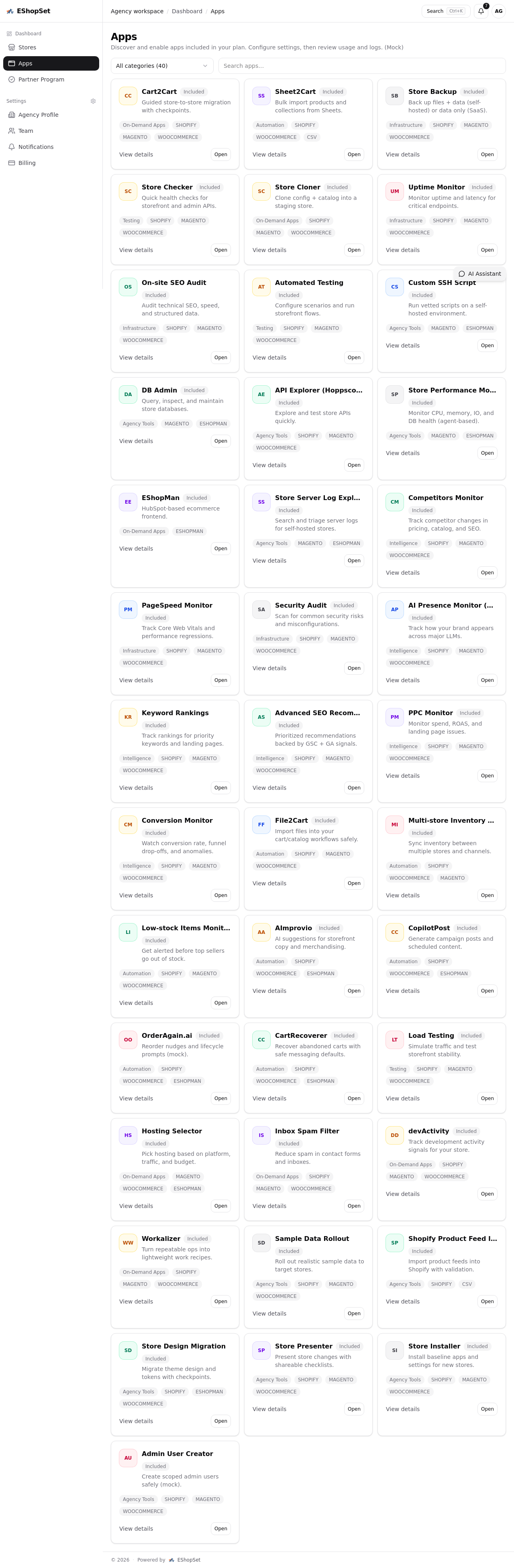
- Continuous Monitoring: Implement tools for continuous monitoring of server logs, file integrity, and WHM/cPanel access.
EShopSet Team Comment
This discussion perfectly encapsulates the kind of critical, real-world issues ecommerce agencies face daily. The immediate action steps outlined are spot-on, emphasizing verification over assumption, especially concerning off-server backups. We strongly agree that robust security protocols, standardized through clear delivery playbooks and diligent task tracking, are non-negotiable for protecting client assets and an agency's reputation. Don't wait for a vulnerability to become a crisis; integrate these checks into your routine client management.
Staying on top of vulnerabilities like CVE-2026-41940 isn't just about protecting servers; it's about protecting your clients' livelihoods and your agency's credibility. By being proactive, implementing strong backup strategies, and using effective task tracking for agencies to manage these complex responsibilities, we can all help ensure our clients' Magento stores remain secure and resilient. Keep these insights top of mind, and let's keep those digital doors locked tight!