Critical cPanel Vulnerability: Protecting Magento Stores and Your Agency's Reputation
In the fast-paced world of ecommerce, agencies are the frontline guardians of their clients' digital storefronts. This responsibility extends far beyond design and marketing; it encompasses the fundamental security of their entire operation. Recently, a critical vulnerability, CVE-2026-41940, highlighted just how quickly a seemingly secure environment can be compromised, posing a significant threat to Magento stores hosted on cPanel environments.
A recent community discussion brought this to light, detailing a scenario that could be a nightmare for any agency: an attacker gaining deep server access and, crucially, deleting client backups before anyone even realizes a breach has occurred. This isn't just a technical glitch; it's a direct assault on client trust, data integrity, and your agency's hard-earned reputation.
Understanding CVE-2026-41940: A Deep Dive into the Threat
The vulnerability, identified as CVE-2026-41940, carried a severe CVSS score of 9.8. While cPanel issued a patch in April 2026, it was actively exploited as a zero-day vulnerability since at least February of that year. This means attackers were leveraging it before a fix was even available, underscoring the urgency for immediate action.
So, what made this vulnerability so dangerous? It allowed an attacker to bypass cPanel authentication through a method called CRLF injection. Once past cPanel, the attacker gained access to WHM (WebHost Manager) – the server's ultimate control panel. With WHM access, the potential for damage was extensive:
- Backup Deletion or Corruption: This was the most alarming aspect. As the original poster in the community thread emphasized, the assumption that server-side backups are safe, even if the store is compromised, was directly challenged. An attacker could wipe out these critical recovery points, leaving merchants and agencies with no recourse.
- Cross-Account File Access: For clients on shared hosting, this meant an attacker could access files across all accounts on the server, not just the target store. This dramatically escalates the risk, exposing multiple clients to data theft or manipulation.
- Server Configuration Modification: Attackers could alter server settings, potentially creating persistent backdoors, installing malware, or further compromising the entire hosting environment.
The core issue here is the ability to eliminate server-side backups undetected, turning a potential data breach into a catastrophic data loss event.
Why This Vulnerability is a Wake-Up Call for Ecommerce Agencies
For agencies managing Magento stores, this incident serves as a stark reminder of the multifaceted nature of security. Your clients entrust you with their livelihood, and a security breach of this magnitude can have devastating consequences:
- Reputational Damage: A data breach or loss of client data can severely tarnish your agency's reputation, making it difficult to attract new clients and retain existing ones.
- Financial Impact: Beyond the immediate costs of incident response and recovery, clients may suffer revenue loss, legal fees, and regulatory fines, which could lead to claims against your agency.
- Operational Disruption: Recovering from such an exploit is a complex, time-consuming process that can divert significant resources from ongoing projects and client work.
Integrating robust security practices into your agency's ecommerce delivery workflow is no longer optional; it's a fundamental requirement. This includes not only technical safeguards but also clear communication protocols and a proactive stance on emerging threats.
Immediate Actionable Steps for Your Agency
Based on the community discussion and expert recommendations, here’s what your agency should check immediately:
- Confirm Host Patching: Directly contact your hosting provider to confirm that the cPanel patch for CVE-2026-41940 was applied across all relevant servers. Document their response.
- Verify Off-Server Backups: This is paramount. Ensure your clients have independent, off-server backups that are entirely separate from their cPanel environment. Solutions like Amazon S3, Backblaze, or dedicated backup services are crucial. These backups must be immutable and inaccessible via WHM credentials.
- Audit WHM Login Logs: Scrutinize WHM login logs for any unusual or unauthorized access during the exposure window (February 2026 onwards) and immediately after. Look for unfamiliar IP addresses, unusual times, or failed login attempts followed by success.
- Inquire About Isolation on Shared Hosts: If your clients are on shared hosting, ask their provider what measures were taken to isolate accounts from other tenants during the vulnerability's active exploitation period. Understanding the extent of potential lateral movement is vital.
Beyond the Patch: Building a Resilient Security Posture
While addressing immediate vulnerabilities is critical, a truly secure ecommerce operation requires a holistic, layered approach. Agencies must integrate security into every facet of their operations, from development to ongoing maintenance.
A Holistic Security Framework for Agencies:
- Layered Security Defenses: Implement firewalls, Web Application Firewalls (WAFs), and endpoint protection. Ensure Magento itself is configured with strong security settings.
- Strict Access Control: Enforce strong, unique passwords and Multi-Factor Authentication (MFA) for all critical systems, including cPanel, WHM, Magento admin panels, and any project management integrations for agencies that touch client data. This includes your HubSpot CRM, Sales Hub, and Commerce Hub accounts.
- Regular Updates and Patching: Maintain a rigorous schedule for updating Magento core, extensions, themes, and all server-side software. Unpatched systems are low-hanging fruit for attackers.
- Secure Development Practices: Implement secure coding standards, conduct regular code reviews, and manage third-party dependencies carefully to prevent the introduction of new vulnerabilities.
- Proactive Security Audits: Schedule regular vulnerability scanning and penetration testing by independent security experts. This helps identify weaknesses before attackers do.
- Incident Response Plan: Develop and regularly test a comprehensive incident response plan. Knowing exactly what to do when a breach occurs can significantly reduce its impact and recovery time.
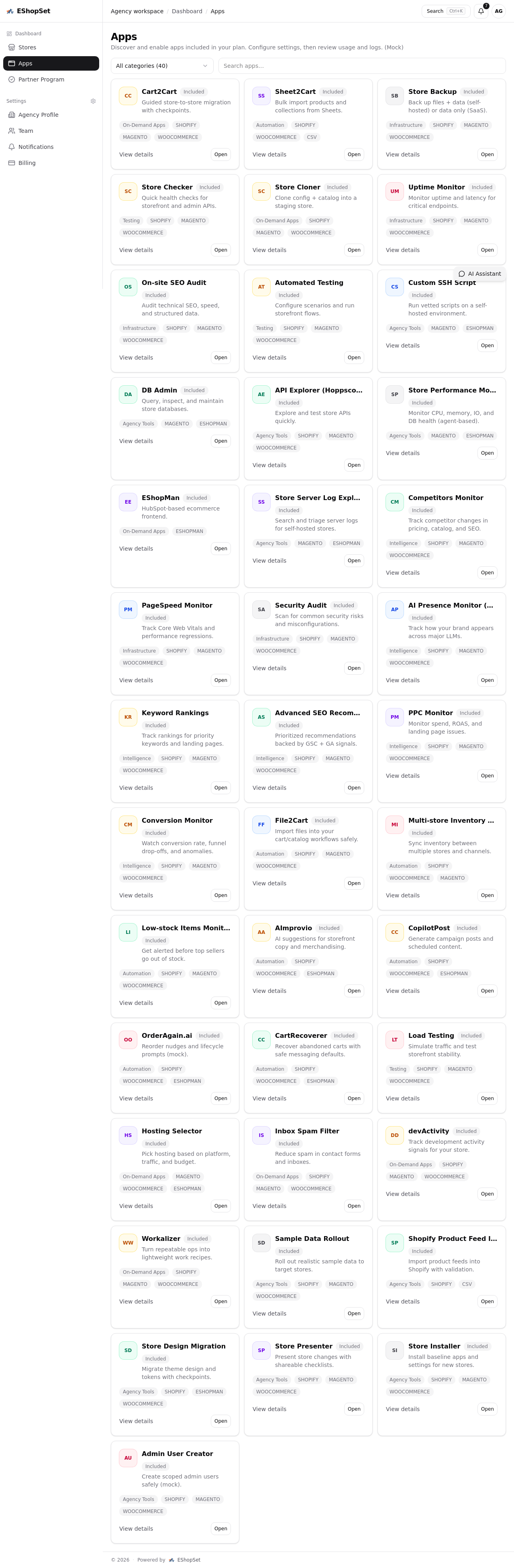
For agencies leveraging platforms like EShopSet, integrating these security checks into your operational workspace is streamlined. Our platform helps ensure that security protocols are a standard part of your ecommerce delivery workflow, not an afterthought. When you're connecting client storefront data to HubSpot's CRM, Sales Hub, or Commerce Hub, the integrity and security of that data are paramount. A robust security posture protects not only the storefront but also the entire revenue operations (RevOps) ecosystem built around it.
Example: Integrating Security into Your Project Management Workflow
Example: Integrating Security into Your Project Management WorkflowConsider a scenario where a new Magento store is being launched. Your agency's project management system, enhanced by integrations, should include security milestones:
- Phase 1: Setup & Configuration
Task: Server Hardening & Initial Security AuditSub-task: Confirm cPanel/WHM MFA enabledSub-task: Verify off-server backup configuration (S3/Backblaze)Sub-task: Implement WAF rules
- Phase 2: Development & Testing
Task: Code Review & Vulnerability ScanSub-task: Automated SAST/DAST scans on new codeSub-task: Manual security review of custom modules
- Phase 3: Launch & Post-Launch
Task: Final Security Check & Monitoring SetupSub-task: Enable real-time WHM/Magento log monitoringSub-task: Schedule monthly external vulnerability scans
This structured approach, facilitated by effective project management integrations for agencies, ensures that security is baked into the process, not bolted on at the end.
Conclusion
The CVE-2026-41940 vulnerability serves as a potent reminder that the digital landscape is constantly evolving, with new threats emerging regularly. For ecommerce agencies, protecting client assets is a core responsibility that demands continuous vigilance and a proactive approach to security. By understanding the threats, implementing immediate safeguards, and embedding a holistic security framework into your operational workflows, you not only protect your clients' Magento stores but also fortify your agency's reputation as a trustworthy and reliable partner in the ecommerce ecosystem.